A new instant messaging app has hit the Smartphone market recently,and is making great news especially after Whatsapp was bought by Facebook, The Name of the Instant Messaging app is Telegram.
What is Telegram/how is it different?
Telegram may be defined as a clone of Whatsapp,with enhanced features,more security and privacy settings and more facilities as compared to whatsapp.
Features :
- Familiar Simple User Interface inherited from Whatsapp.
- Group Chat can be done simultaneously with 100 people. [Whatsapp maximum limit is 50]
- Allows sending of Documents and files. [Whatsapp doesn’t allow any documents/files sending]
- Photos and Video sending size upto 1GB. [whatsapp limit 512MB]
- Open Source and Cloud Based.
- Allows you to change your privacy settings,last seen,etc.
- Messages are encrypted with highest standards and no logs are saved on the server so your chats are completely private!
- Still, if you are not happy you can even send Encrypted QR messages which only can be decrypted by the Receiver..
- And All these features are Ad-Free and Free to Use forever,unlike Whatsapp which charges Subscription Fees…
So, Now 3 Ways you can install and Use Telegram on PC
Way – I
- TDesktop [Telegram for Windows] [Windows/Linux] : tdesktop is unofficial Telegram Client for Windows, it comes with a simple setup file, which you can download and setup as any other windows software by specifying directory and clicking next,next!, your telegram for windows [tdesktop] will be installed ,and you can now put number and register. Linux users can use it directly in Wine! it works on all versions of windows 7/8/8.1/XP
Click here to Download the Telegram for Windows Client / TDesktop
Instructions :
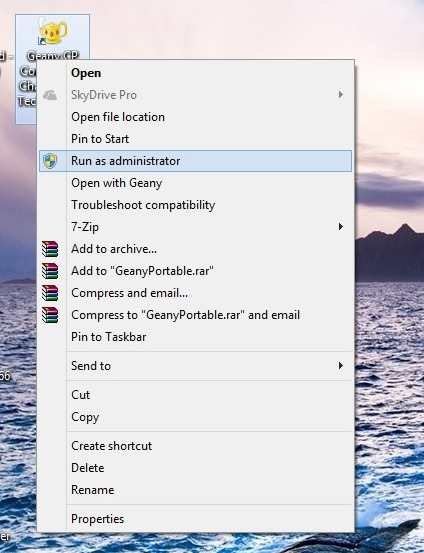
now you can locate the shortcut on your desktop. Open the telegram PC app, and..
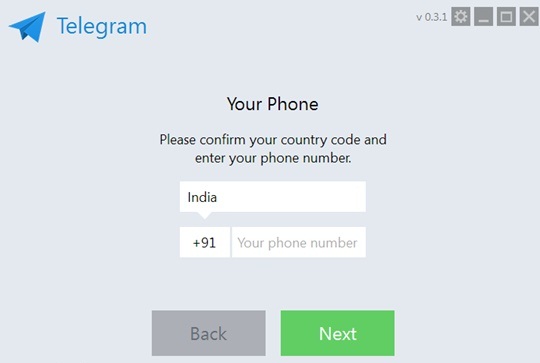
 Now, Enter your Country Code and Mobile Number and Click on Next, you will receive verification code on your number, now put it inside the tDesktop App and yo! you can start chatting using Telegram
Now, Enter your Country Code and Mobile Number and Click on Next, you will receive verification code on your number, now put it inside the tDesktop App and yo! you can start chatting using Telegram
Way – II
2.Google Chrome Extension/ App [Windows/Linux/MAC/Chrome OS] : If you are not interested in installing the tDesktop client and want to use Telegram in Google Chrome, you can do it too, just install the Webogram Chrome extension from here and follow the same mobile number verification steps to use Telegram.
Click here to Download/add Webogram [Telegram] Google Extension/App
Way – III
3. in your browser Direct/Simple URL [Window/Linux/MAC/Chrome OS] : Now if you feel lazy and don’t want to install neither Windows client nor Google Chrome Extension , you can Simply type or Go to this Online Webogram URL to load Telegram directly in your Browser!! Simple and efficient isn’t it ?
Go to this URL to load Webogram right in your Borowser
http://zhukov.github.io/webogram
or you can CLICK HERE to load Telegram in your Browser itself!
here’s a glimpse of Telegram in my Browser : Google Chrome
So, Lets Enjoy this New,and Opensource Messaging app 🙂 Do like and Share this post if you liked this, else if you have any complaints/suggestions or require any help Feel free to comment 🙂




![Installing and running Microsoft Visual Basic 6.0 On Windows 7/Windows 8 [x32-x64 : 32bit-64bit] with all features!](https://techapple.net/wp-content/uploads/2013/10/install-vb6-on-windows7.png)
 fortunately,this Problem will Be Solved by simply clicking the Run Program and the Setup Started.. 🙂 , as you are running the setup,its possible that setup might become too very slow on places such as “searching for installed components” , “finishing installation” etc..dont worry its,totally normal! just wait for the setup interface to come up 🙂
fortunately,this Problem will Be Solved by simply clicking the Run Program and the Setup Started.. 🙂 , as you are running the setup,its possible that setup might become too very slow on places such as “searching for installed components” , “finishing installation” etc..dont worry its,totally normal! just wait for the setup interface to come up 🙂

 Now you will see a black terminal as shown in the below figure,now for writing the program in gnu octaves, simply type as”edit <your program name.m>”
Now you will see a black terminal as shown in the below figure,now for writing the program in gnu octaves, simply type as”edit <your program name.m>”