Personalized Data Cloaking by AutoGraph Review | Best And Easy To Use Tool
Share
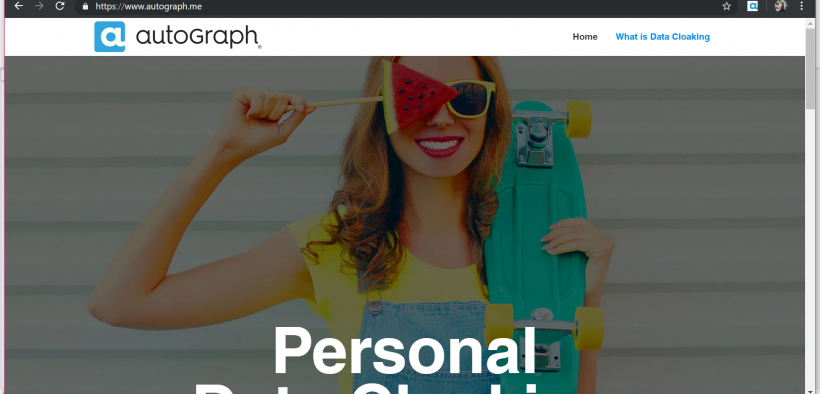
The 21st century came with a tsunami of customer-friendly services, smart devices, artificial intelligence, and websites, and with that came the hurricane of cybersecurity breaches, and spam emails. The moment you connect to the internet, the danger of your information being misused is dominant. So, what should we do? Boycott all websites? Never use any personalized web service? AutoGraph. comes with all the answers that you would need to solve this issue. They use the Personalized Data Cloaking method, which is a one-stop solution to your privacy problems.
What is cloaking?
Cloaking means to disguise or hide. Personal data cloaking service conceals your online identity, which helps you utilize and personalize all the online content without revealing your personal information. This feature saves you from privacy threats or cybersecurity breach. For instance, consider a web service that can only be used by signing up using your email. The fear of misuse of information and spam emails might discourage people from using this service. Personalized Data Cloaking would generate an alternate email identity specifically for this website and retain the information making it easier to log in in the future and save the progress.
How to use this service?
AutoGraph has made it extremely easy to use this identity cloaking feature. For your easy, I already downloaded and used it so I can explain to you in depth. Just follow these steps and you will be good to go:
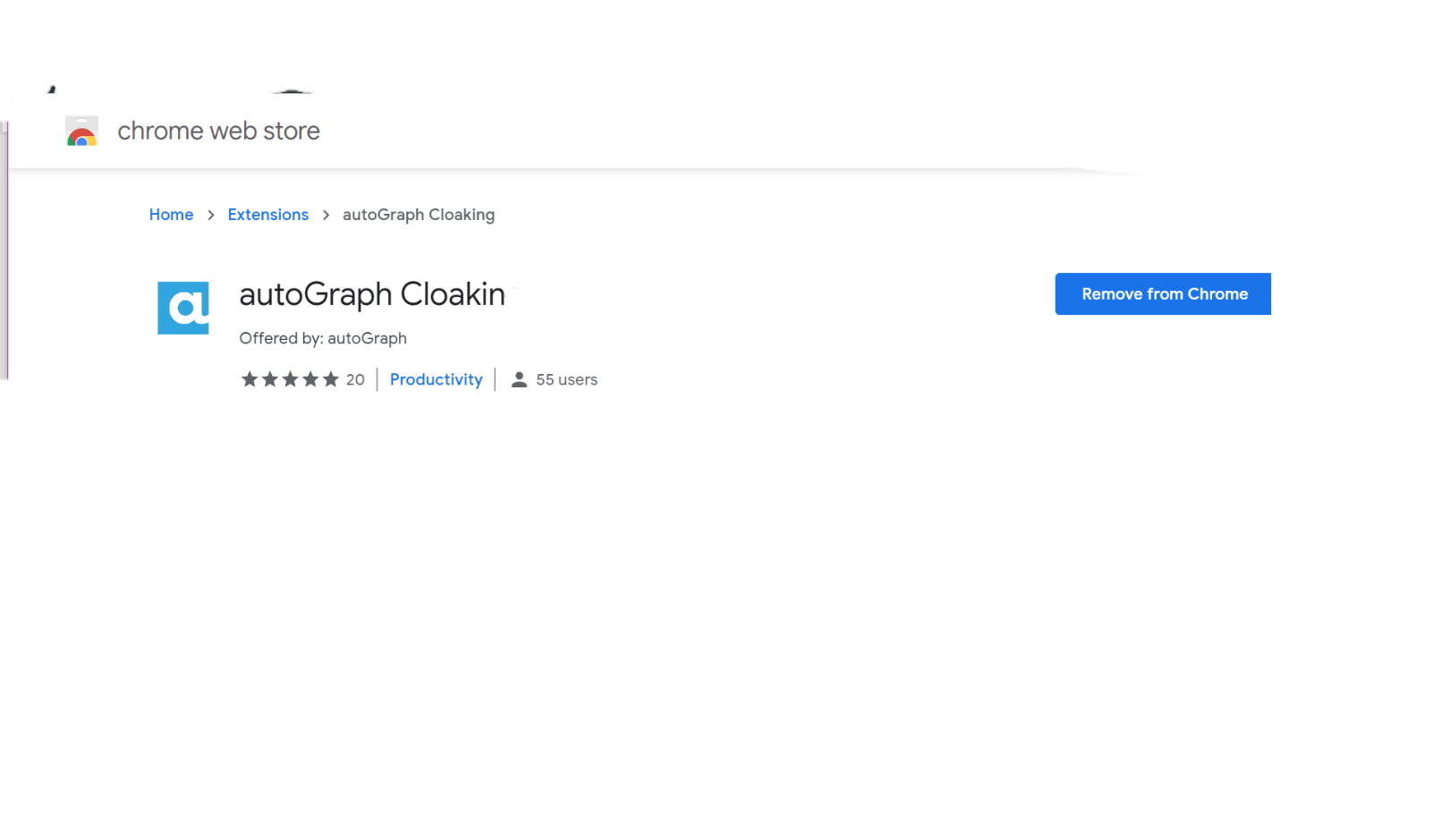
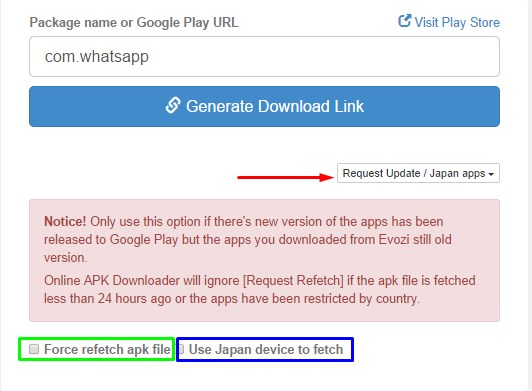
Step 1: Download autoGraph feature cloaking from the official store and add to your server.
Step 2: Click on the extension on the bar and use the sign in option to create an account.
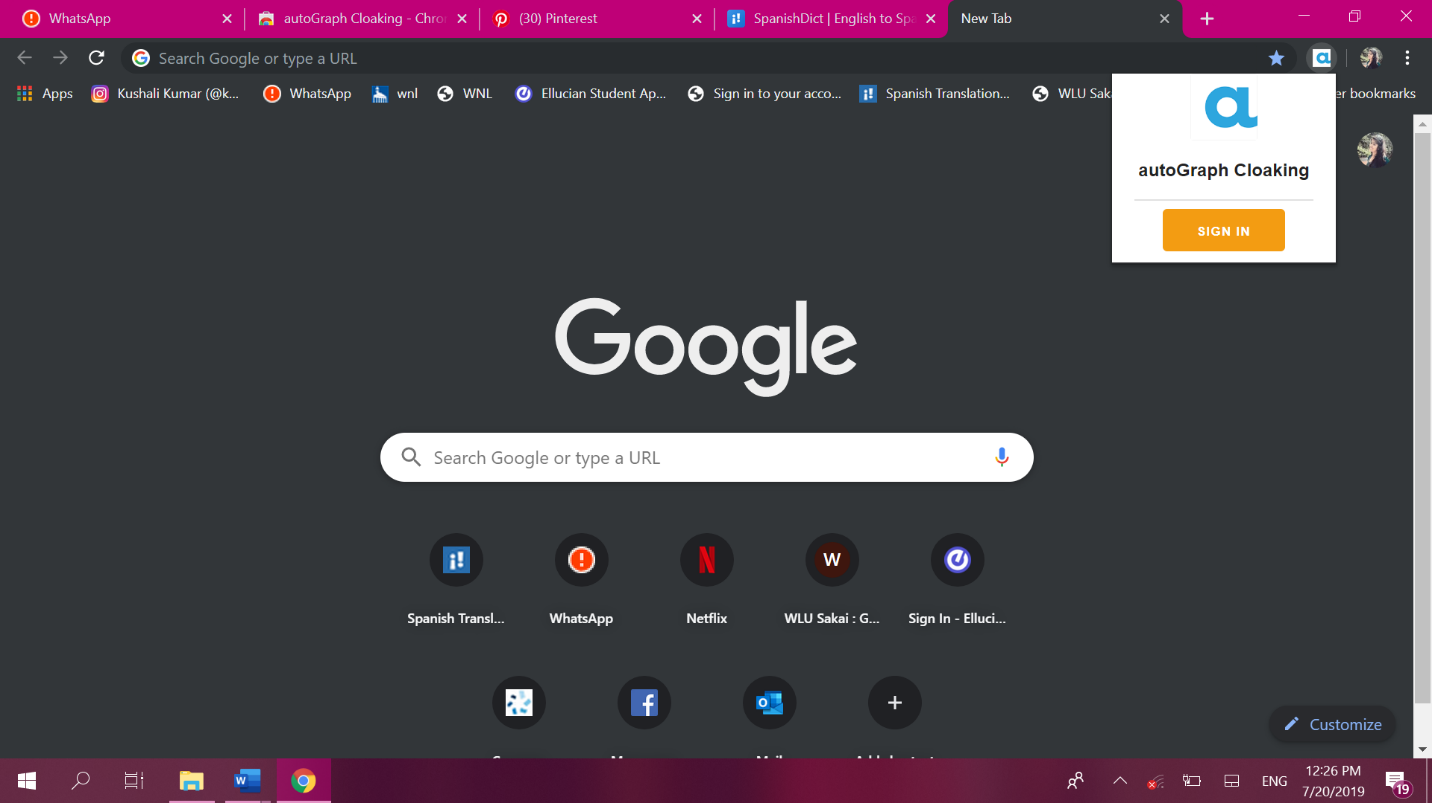
Step 3: use the Log in with Google option to create a new account.
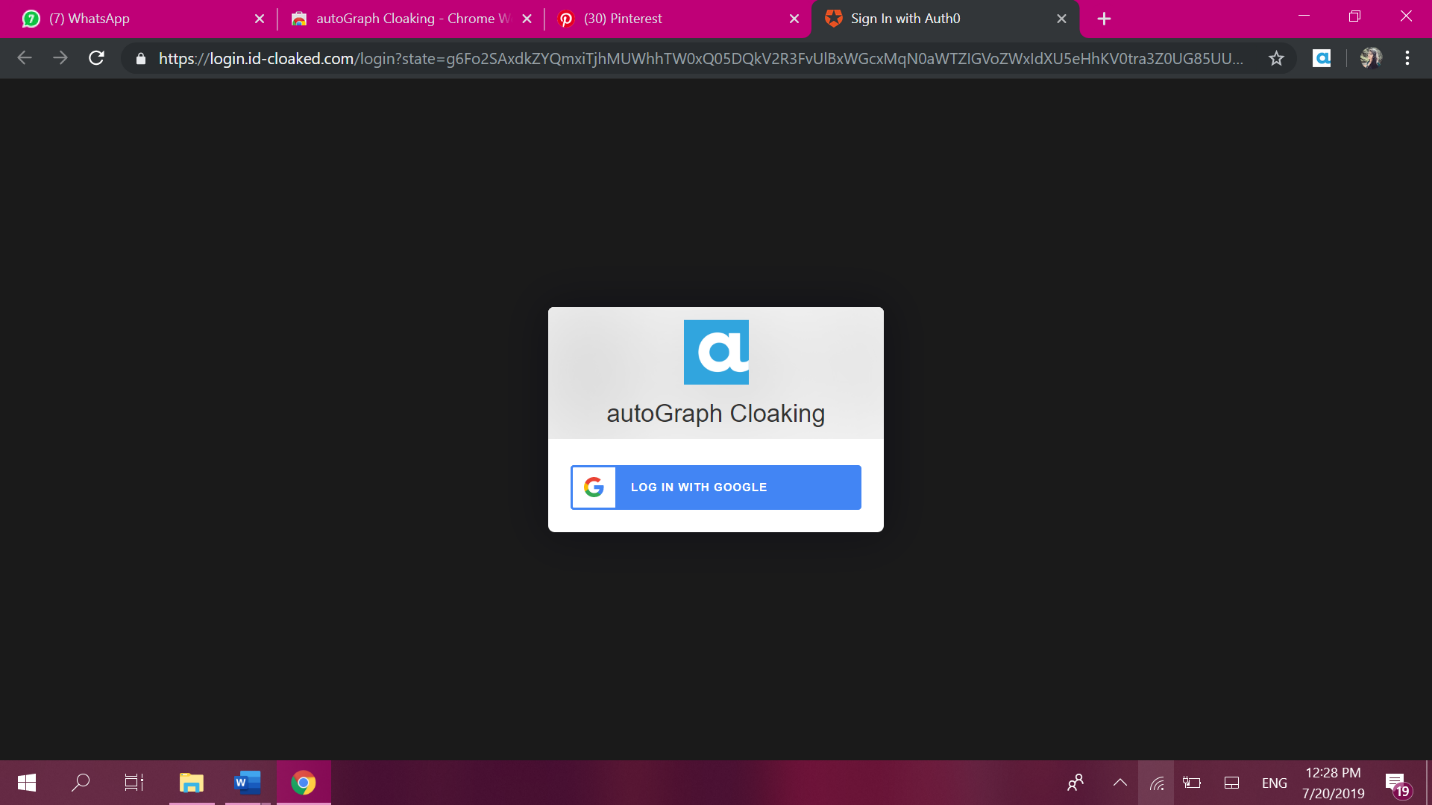
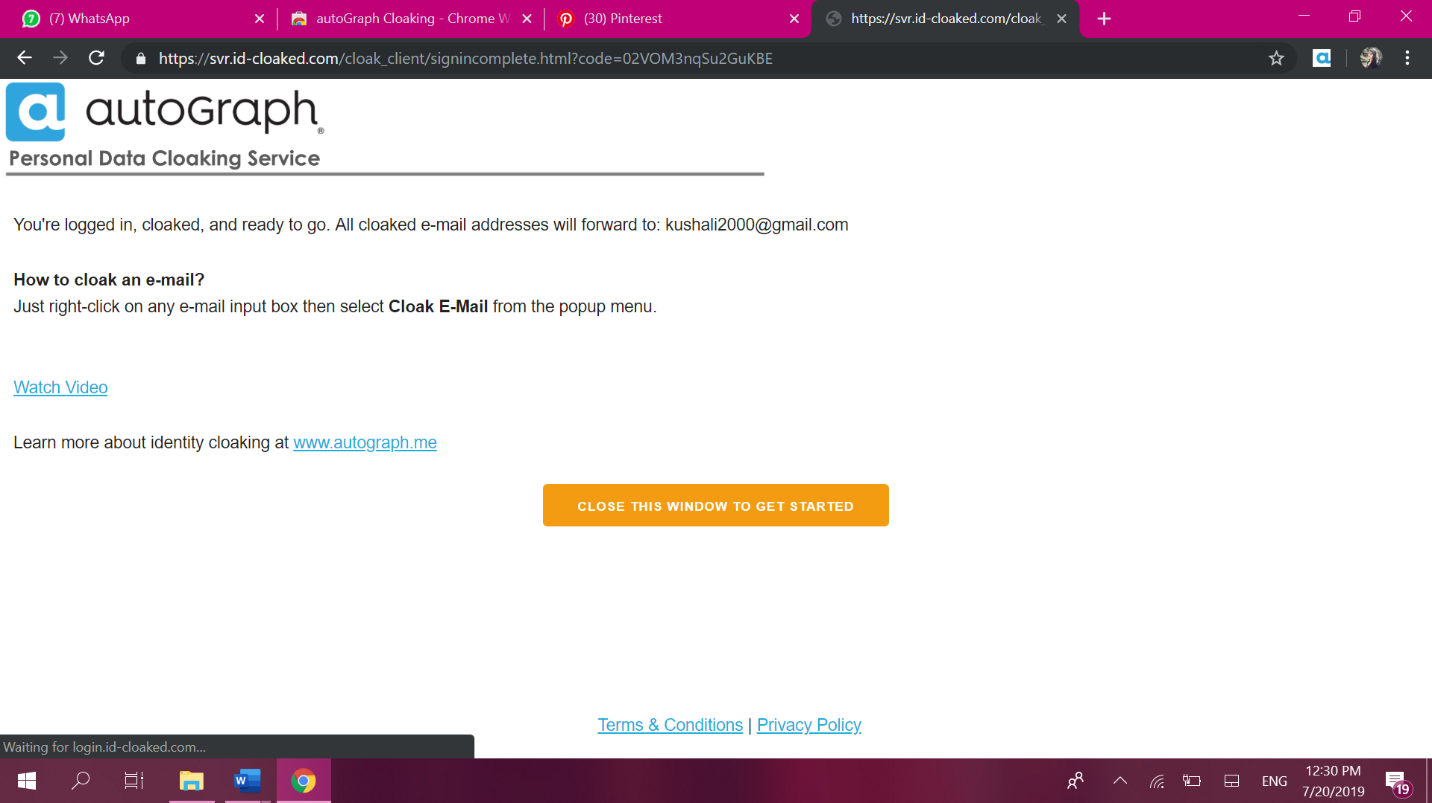
Step 4: To make it easier and more transparent, they have attsched a video and link to explain the functions better to the customer. After watching this, chose ‘close the window and get started’.
After this you are good to go. It was that easy.
Now how do I use this to create a pseudo account?
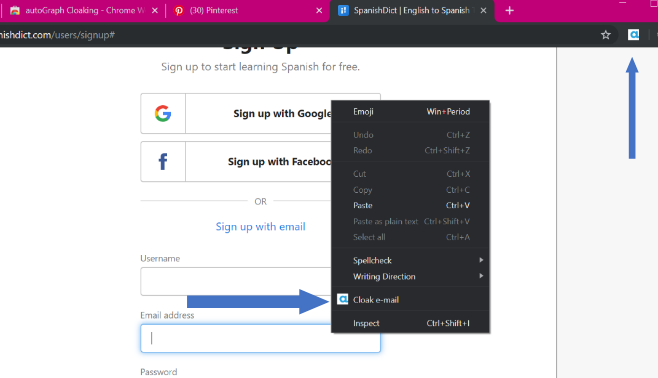
Don’t worry, I got your back. Whenever you wish to prevent your identity, right-click and press ‘cloak email id’, as shown in the image and your private information would be completely safe. If they require a conformation, that email would be redirected to your google email id, keeping your privacy intact.
Whenever you return to the same website, you can click on the symbol and open the ‘Manage Cloaked IDs’. This would show you a list of all the cloaked IDs.
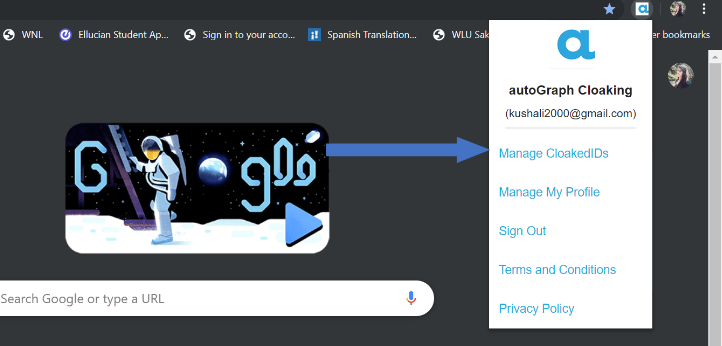
Just copy the email with that website and the same pseudo-identity would be used to log in, saving your past progress and personalization.
Controversies?
In the past, cloaking (search engine optimization technique) has been misused by various websites wherein the content presented to the search engine spider is different from that shown to the user’s browser. This misdirection is created by delivering content based on the IP addresses or the User-Agent HTTP header of the user requesting the page. For example, the user clicks on a link to educational or cartoon website, and instead redirected to a pornography website. This redirection could not only be traumatizing to the user but also spoil their trust and online experience, especially in the case of children. However, the autoGraph uses this technology for the benefit of the users and is in no sense harming the host website.
AutoGraph’s launch of this identity cloaking feature comes as a counter to Apple’s ‘Sign in with Apple’ feature. The increased awareness about privacy threats, due to the Facebook and Alexa controversies, has been a great encouragement for the users to make the switch to the cloaking service. AutoGraph plans to, in the future, increase the scope of this cloaking service by adding the cloaking phone numbers and addresses feature, all of this completely free of charge. Only time will tell how the audience and the critics receive them.